
As more detailed information about Russian hacking attempts in our elections has emerged, the question is whether our elected officials at all levels of government represent the choice of the majority of citizens. This is a basic credo of our form of representative government; that each and every citizen should have one vote and the candidate with the majority of voters wins. The elected official is then expected to take into account the interests of the whole community, regardless of whether they supported him/her; to represent all members of the community for the benefit of the whole community. The system has been badly undermined by the dictum that the dollar equals a vote; the interest with the largest pot of gold has the biggest voice. PAC money out shouts the citizen with the result that average Joe and Jane can’t get in a word edgewise. For elected officials, the interests of the whole community has morphed into the interests of my campaign funders, no matter how the general populace feels. For the Republicans, campaign funders translates to the Koch clatch.
All voting is local. Electoral systems are generally managed by county or state officials. This leads to a voting process that varies from county to county, which can be a strength in defense against an organized attack. In a system that is composed of widely dispersed nonuniform entry points, pinpointing strategic strikes is complicated and requires multiple actions, depending on the desired objective. On the other hand, election agencies are generally poorly financed and staffed, without expertise in internet technology or internet security; polls are staffed by older volunteers with even less IT savvy. They are underfunded, with aging equipment and software that will require a major infusion of cash and security expertise that many cash strapped state budgets can little afford. This may leave the voting process vulnerable in this day of sophisticated computer hacking especially because of the hyper-partisanship that surrounds every issue.
While not wanting to contribute to the generalized anxiety surrounding the US voting process, it is a fact that Republican party dirty tricks at the polls over the last decade have significantly changed the political landscape, quietly disenfranchising millions and millions of voters across the country. The influence of those purged voters, overwhelmingly minorities, could ultimately have affected the 2016 electoral college totals because numerous narrow state margins propelled Trump to victory. This is extraordinarily important because unlike Russian interventions, we can take action against this kind of activity to reclaim our democracy. Americans are free to make dumb mistakes and if a legitimate majority of the country is satisfied with the Trump administration, then so be it. At the same time, future candidates who oppose Republicans must have an equal possibility of winning electoral office in a fair fight.
 Let’s first look at Moscow’s cyber hacking adventures. The FBI reported in August 2016 that hackers had been probing voter registration databases in almost 15 states. Georgia was not one of those states, although there is probably no way to know that given poor security safeguards and the state’s refusal to allow outside review of the system or assistance from Homeland Security to investigate or assist with security enhancements. Georgia’s story is instructive because it uses paperless voting machines like several other states which are both old, circa 2002 and known to have serious security concerns. However, state voting system officials are regularly asked to educate other states and even foreign countries.
Let’s first look at Moscow’s cyber hacking adventures. The FBI reported in August 2016 that hackers had been probing voter registration databases in almost 15 states. Georgia was not one of those states, although there is probably no way to know that given poor security safeguards and the state’s refusal to allow outside review of the system or assistance from Homeland Security to investigate or assist with security enhancements. Georgia’s story is instructive because it uses paperless voting machines like several other states which are both old, circa 2002 and known to have serious security concerns. However, state voting system officials are regularly asked to educate other states and even foreign countries.
Georgia uses a single model of voting machine throughout the state, unlike most states that use multiple different models. These touch screen machines, made by the now defunct Diebold become Premier Election Solutions, have been in use since 2002. The company also made the associated software for the state’s ExpressPoll poll books which are the electronic devices used by poll workers to verify that a voter is registered before allowing them to cast a ballot. Additional software maintains the databases for the GEMS servers that are used to prepare paper and electronic ballots, tabulate votes and produce summaries of vote totals. The software version currently running on machines was last certified in 2005 and is running on Windows 2000 that hasn’t been supported by Microsoft for at least 5 years. In addition, unlike most states where management of elections is decentralized in individual counties, Georgia’s system is centralized to a center which manages balloting and machines for all the counties.
That center is the Kennesaw State University Center for Election Systems which is responsible for testing and programming all the voting machines for the state of Georgia. The Center is responsible for maintaining the machines and the software used by the machines as well as providing the support for the GEMS servers also distribute the electronic ballot of definition files that go into each voting machine before elections. These files tell the machines which candidate should receive a vote based on where a voter touches the screen. If these files were altered, the machines could record votes for the wrong candidate. Since Georgia machines have no paper trail which could allow voters to verify their choices before ballots are cast and could also be used to compare against electronic tallies during an audit, officials might never know the machines recorded votes inaccurately. There is no way that officials would be able to determine if this has ever happened, according to computer security experts. The Center has remained a staunch advocate of Premier/Diebold voting machines despite numerous reports by computer security experts over an extended period time including a 2007 video showing how to introduce a virus into the voting machine.
One other software system the Center uses is content management software, Drupal. Drupal is a significant problem; the Center is running an ancient version, which had not been updated, despite a well known critical software vulnerability known since 2014. The patch to prevent attackers from easily seizing control of any site had been available for over 2 years, but gone unused by the center despite the widely known existence of automated hacker scripts to attack the Drupal vulnerability.
Much of Georgia’s voter machine security depends on absolute separation from the internet. The system operates on a series of separate servers that, at least in theory, cannot be connected to the internet and therefore can not be hacked. The ExpressPoll poll books are delivered to workers on CDs, a process that could have easily been compromised when one county officials car was vandalized and the CDs stolen. The state contends that no data was stolen although they gave no details on the methodology used to determine that.
When Homeland approached the secretaries of state with the news of Russian meddling, Georgia’s secretary of state Kemp was naturally one of those who reacted badly. So when news broke of a data breach at the Kennesaw State Center in March, he accused the FBI of maliciously attempting to hack Georgia systems. An investigation did reveal an intrusion, in which state officials wrongly reported that millions of voter records were stolen. In reality, it was a second intrusion to check on whether there had been any security changes after an earlier one in August 2016. At that time, a curious cybersecurity researcher interested in voter system security after the FBI reported hacking in multiple states accidentally downloaded 15GB from the center’s website using a simple script to explore the site. The files were supposed to be protected by a password protected firewall but the center had misconfigured the server so anyone could access them from the root. That 15G included registration records of 6.7 million voters, instructions and passwords for election workers to sign in to a central election server on Election Day and software files for the state’s ExpressPoll poll books, the electronic devices used by poll workers to verify that a voter is registered before allowing them to cast a ballot as well as databases for the GEMS servers that are used to prepare paper and electronic ballots, tabulate votes and produce summaries of vote totals. This was evidence that the wall between the internet and the voting system had been breached at some point, even if they were not continuously and currently linked.
When the researcher approached the Kennesaw Center director before the November elections, he simply blew him off. Merle King, the executive director of the Center, thanked him and said he would have the server fixed but threatened him not to reveal the information to anyone, especially the media. King never informed Kemp’s office and took a piecemeal approach to the repair, leaving the unencrypted http version of the Drupal still vulnerable, as a friend of the researcher later discovered in March 2017.
When news of a system intrusion at the Center surfaced 6 months after the cyber researchers discovery, the Kennesaw University IT Services, the secretary of state’s and governor’s offices and later the FBI all launched investigations. In the course of investigation, it became clear that the Center had been operating its networks outside the scope of the university and secretary of state’s office for years, essentially unaligned with any larger security strategy. In addition, although the Center had separate public and private networks, a public network jack sat in the closet with the private network, opening up the possibility that workers could have connected the private network system to the internet. Workers had also installed their own wireless access point in the office, a potential entry point into the network for hackers. The evidence pointed to a knowledge deficit on the part of the center’s small staff, some of whom are non-technical students at the university. The presence of the GEMS files on an internet connected server is a significant piece of evidence that points to previous connections between the private and public systems. All indications suggests that Georgia’s voting system is extremely vulnerable to hackers of all descriptions and that the integrity of the state’s vote is in serious jeopardy.
Georgia’s secretary of state Kemp insists that the Premier/Diebold machines met federal standards, adopted under 1990 federal guidelines, when it was adopted in 2002. Kemp says that when the system met 2015 certifications it met requirements under state law although new federal guidelines have been issued. Security experts say the certification is too old and that the combination of two different certifications is outside the norm. The machines are regularly tested before and after elections, but here again, a security expert knowledgeable about the machines suggested that state testing is a bit like asking the machine itself if it’s results are accurate without any outside corroboration. He has been able to corrupt machines in the lab with malware that would be almost undetectable during regular operation.
Kemp also seems to have an aversion to security experts. Georgia was one of two states to reject the offer from the Department of Homeland Security to assist states with securing their systems. In fact, he accused the FBI of nefariously hacking into Georgia’s system. The previous secretary of state, Karen Handel who is now the 6th district Congresswoman, ordered a security review of the voting system to fulfill a campaign promise. The Georgia Tech team found a number of security concerns, even though they were denied access to the Kennesaw Center network or review of its security protocols. Handel who did not insist that the Center’s comply with requests for access to the Center, did insist that the report itself state that they did not have enough information to evaluate security safeguards. Even with that, she buried the report. The obvious conclusion is that the secretary of state and the center are hiding something, and it may be more than just security. For instance, there was the “glitch” in some Cobb county precincts memory cards in the recent 6th district special congressional race. But when the issue was supposedly resolved, Ossoff, the Democrat, fell from 53% of the total vote to 49% and stayed there, setting in motion the runoff with Handel, the Republican. In the absence of paper ballots, there is no way to know if votes were changed or categorized as “inconclusive” or thrown out.
Here are some examples of voting system vulnerability. If hackers were to delete voter names from the database stored on the center’s server or alter the precinct where voters are assigned, they could create chaos on Election Day and possibly prevent voters from casting ballots. This is not idle conjecture; in 2016, a glitch in the ExpressPoll software led some voters in Fulton County to be told that they had arrived at the wrong precinct but when redirected to a different one, they were told to return to the original precinct. Beyond that, a rogue memory card or unsophisticated poll workers could introduce malware from phishing emails in individual machines which is likely to go undetected under current security operations.
To summarize, voting machines throughout the state of Georgia are controlled by a small university based center with lax security and no indication that they have any interest in changing that. They are unlikely to try to remedy a problem that they refuse to acknowledge. The voting machines are 15 years old, using multiple outdated software systems running on an outdated operating system without the capability to use the latest security safeguards. The Center has refused to update the systems with known security patches. The absence of any paper ballots makes it impossible to verify election results or investigate reports of voting irregularities. The pretense that these ancient computer systems running on outdated software can be made secure against sophisticated hackers is clearly absurd. Officials have also demonstrated a lack of will to create a secure system and a propensity to resist any independent expert assessment and improvement in security, let alone the ongoing security watchfulness required in these days of advanced hacking. That may reflect the mindset of state officials where large swatches across the state lack wireless access. The optimal solution is to upgrade the whole system, with voting machines with paper ballots and current generation software and management systems. If Georgia is an ideal model, our election system demonstrates a partisan pigheadedness to remain vulnerable to multiple threats, not just the Russians.
It’s worth examining to a fuller extent federal knowledge about the Russian electoral interventions in the 2016 election. On a primary day in June 2016 in Riverside County, California the district attorney’s office fielding a lot of complaints that their registrations had been changed without their knowledge from people attempting to vote, sent investigators to polling places. Most had cast provisional ballots. In the following days, there were more people who came forward with the same complaints. Investigators concluded that the changes had been made by hackers using private information like social security and driver’s license numbers to access the central voter registration database for the entire state. Unfortunately, the state system did not capture the IP addresses of the computers that had made the changes so the trail went dead. Opposing political responses were predictable; the Republicans thought the Dems were trying to suppress GOP votes in the overwhelmingly Democratic state. The Dems thought their opponents were trying to excuse their losses. And there it was; public faith in the electoral process had been dented and as it dawned on federal investigators later, that was the point.
Cybersecurity experts considered it a test run to see what kind of election day havoc could be generated. Riverside was the first evidence that the Russians were mounting an aggressive campaign to undermine Americans’ faith in their own democratic process. The Obama administration struggled to craft a response while unearthing the full extent of Russian efforts. After resistance at the state level to federal investigation and assistance with improving system security, the hyper partisan reaction of Republicans threatening to politicize the election convinced Obama, probably mistakenly, to back away from announcements to the public. With their hands tied, officials decided there was nothing they could do to prevent the cyber activity and settled on a plan to react to cyber incidents on election day that would first defer to the states, but included armed federal law enforcement agents to polling places if voting was completely blocked and to call out military and national guard forces as requested in the presence of violence. For up to 3 days after the voting, an interagency force would address any further internet intrusions including “planted stories calling into question the results.” Proof of Russian success are Gallup poll results that only 30% adults were confident in the honesty of our elections and 69% were not.
Current Russian attacks on elections extend back to at least 2008, when both Obama and McCain campaigns were hacked. But the attacks used to be ephemeral, with the culprits quickly exiting the systems. The summer of 2016 saw more attacks in Arizona and in Illinois, a hacker uploaded a malicious code that allowed access to all 15 million past and current voter files for the previous 10 years; he/she stayed for 3 weeks, without being detected. When Illinois discovered the cyber intrusion in July, the FBI Cyber Action Team (CAT) was able to determine that 90,000 files were stolen, the majority of which had social security and driver’s license numbers. But more importantly the hackers tried to change/delete information in the voter rolls. The techniques and digital footprints convinced the FBI that this was the work of Fancy Bear, an arm of Russian military intelligence (GRU).
The FBI worried about a nightmare scenario in which Russians would actually be able to affect elections results. Ed Felten, the voting machine expert well acquainted with the susceptibility of touch screens, could foresee a compromised poll worker, possibly through phishing, providing outside access to machines before election day. That process would be extraordinarily tedious way to impact a final result, without information about which precinct would be critical to the results. It is worth noting that Jared Kushner could theoretically have been a critical connector in his role overseeing campaign media communications. Knowledgeable experts have marvelled at the campaign’s precinct level pinpoint accuracy use of targeted social media. The campaign is known to have used Cambridge Analytica, a consulting firm funded by ultra conservative billionaire Robert Mercer, which specializes in strategic communications using data mining. Access to those kinds of data, either through consent or through stealth could have easily improved Russian efforts. Kushner’s testimony is high stakes, but, given the family history, unlikely to be truthful.
How did the Russians get so good is a real question. A few years ago, John Podesta was a mystery to them and they had no knowledge of the DNC. No one on Capitol Hill took the Russians seriously; they were considered among the most ineffective lobbyists in Washington because they didn’t know who to approach and when. Fast forward to 2016, when they were coax voters in Ohio and Indiana into watching stories on Russia Today, a state owned Russian TV network and strategically target districts in Florida with anti-Clinton propaganda. Ultimately, the steady drip of fake news that discredited Clinton- she has Parkinson’s, she has pneumonia, she’s tied to sex trafficking in a pizza shop, etc – exploited perennial suspicions that she was duplicitous and could not be trusted. These efforts probably continued to depressing voter turnout for Hillary except for those who were anti-Trump and didn’t want go the independent route. How did Moscow know when and where to release different pieces of information?
The FBI team did create some possible intrusion scenarios that would not appear obvious but could be disruptive. Simply flipping a letter in every voter’s address would mean that every voter in a swing county would have to use a provisional ballot, creating panic which could then be exploited by a propagandist questioning the election result, or in the current climate, suggesting that one of the parties intentionally tried to manipulate results. Even less complicated, a YouTube video showing the hacking of a single voting machines with dialogue that claims it was one of only 10,000 without actually doing it even once – real fake news- could create panic in every precinct, trigger investigations and undermine any final vote count.
The DNC hacking and Wikileaks email release provided political fodder for the CelebrityCandidate to exploit across the media, including his appeal to Russia to hack Clinton’s email server, in part to distract from the first report of Russian hacking. In classic Trump form, he accused the Dems of what he thought the reports of Russian hacking implied; that the elections were rigged. Even in those early days, a core of Trumpophants were willing to believe whatever he said, no matter how contradictory or implausible. So when Homeland Security Secretary Jeh Johnson approached state election officials in a conference call on August 15 about declaring elections part of US critical infrastructure, he was surprised that some states called foul over the “overreach of the federal government” rather than patriotic indignance at the threat from a hostile country he expected. The designation would have given the feds access to state-level voter information. The Pavlovian Republican response was State Liberty or Die!
The White House had already seen partisan political pushback from Congressional leaders. In closed meetings, the Democrats reacted with patriotic dismay and wanted to explore responses. Mitch McConnell had the completely opposite, self interested reaction and threatened to broadly politicize the accusation as an attempt to undermine the Trump campaign. He wanted to use “Russians are helping Trump” as chum in the water to attract the sharks at Trump rallies to bloody the race through the conservative right Breitbart-radio-blogs-Facebook+ Twitter fake news sphere.
Obama, always careful to weigh the pros and cons of each position, conjectured that an aggressive countermove against Russia could have been met with an outright cyberwar and domestically, exacerbated raging anti federal government sentiment now interpreted as partisan maneuvering for Clinton. In the interim, Moscow had stepped up its game, with intrusions in Florida, New Mexico, Tennessee. Before the election, they had meddled in 25 states and had tried to hack all 50. By July of this year, an NSA report confirmed that Russian hackers had employed an extensive phishing campaign to hack election officials as well as targeting voter registration systems. Bloomberg also reported that hackers had targeted voter registration systems in 39 states and had tried to delete or alter voter data in at least one state. They had also accessed software used by poll workers to verify voters at the polls similar to the type used in Georgia.
After Obama had a harsh word with Putin in China, it seemed Moscow may have simmered their attacks while some states were trying to beef up their security, some even used assistance from Homeland. There were a few cyber incidents, but no large coordinated Soviet effort, at least none that was detected. The FBI worried that they were only detecting the clumsiest of Russian hackers and the more adroit were going undetected. But in October, the Russians hackers attacked the company that provides election software and machines for 8 states, using that to create an email for a phishing campaign against elections officials nationwide. So, the intelligence agencies fell back on a modified response plan and kept their fingers crossed. Admittedly, much of the investigative work done by the FBI was delayed until after Clinton had lost the presidency. Still the response of the Republicans, jubilant in victory, was to follow the lead of their fearless leader in complete denial until a growing amount of evidence has now forced them to acknowledge the Russian threat as they try to exclude the possibility of campaign collusion. Denial is firmly embedded in GOP DNA safeguarded by a refusal to allow investigation, as is apparent in Georgia which is probably more vulnerable than other states that are more decentralized. (Read the Time magazine article “The Secret Plan to stop Putin’s election plot” at http://time.com/magazine/)
 Donald Trump has promised to restore the country’s faith in elections, a faith that he was instrumental in destroying during a campaign where he consistently insinuated that the results would be rigged if he lost. He went as far as suggesting that he might not accept the elections results. Strangely, he concluded that the electoral process was indeed intact when he won, but his win, history making in his mind, was tainted by 3 million illegal voters who all voted for Clinton. Of course this fit neatly into Republican propaganda that has been charging voter fraud since Obama’s stinging victory in 2008, as a pretense for machinations that would restrict voters to those who support their party. Their instrument has been state voter IDs laws, literally written from templates distributed to state legislatures by The American Legislative Exchange Council (ALEC), a conservative organization financed by the Koch brothers. Legislatures have targeted minorities, the poor, the elderly and the young, groups that typically vote for Democrats and voted overwhelmingly for Obama in 2008 (oleblacklady/It turns out voting is a privilege).
Donald Trump has promised to restore the country’s faith in elections, a faith that he was instrumental in destroying during a campaign where he consistently insinuated that the results would be rigged if he lost. He went as far as suggesting that he might not accept the elections results. Strangely, he concluded that the electoral process was indeed intact when he won, but his win, history making in his mind, was tainted by 3 million illegal voters who all voted for Clinton. Of course this fit neatly into Republican propaganda that has been charging voter fraud since Obama’s stinging victory in 2008, as a pretense for machinations that would restrict voters to those who support their party. Their instrument has been state voter IDs laws, literally written from templates distributed to state legislatures by The American Legislative Exchange Council (ALEC), a conservative organization financed by the Koch brothers. Legislatures have targeted minorities, the poor, the elderly and the young, groups that typically vote for Democrats and voted overwhelmingly for Obama in 2008 (oleblacklady/It turns out voting is a privilege).
Trump’s new commission, voter rolls in hand, will likely create evidence of fraud – fake facts- and roll out a blueprint for states to further disenfranchise minorities. But behind the published results, they may create an infrastructure that will allow Republicans to purge voters quietly from voter rolls or invalidate votes at the polls, much like they did when Bush 43 signed the Help America Vote Act, which required all voting to be electronic.
So Trump has decided nonwhites are the new threat to fair elections, but the actual threat to voting, Russian cyber intrusion, he has not fully acknowledged, even in the face of evidence from every other European democracy, presumably not Clinton allies. As the secret Russian contacts multiply across the Trump campaign and administration, it is increasingly difficult to continue to give the benefit of a doubt to the Donald. Trump may indeed be a Manchurian candidate. As I’ve said before, we are living with the damage done in the last election and Putin has Trump eating out of his hand internationally. Moscow may just call off future interventions. What else does Putin need? So far 45 exacerbated voting system vulnerabilities by trying to defund the EAC; the Democrats have responded by introducing a Senate bill to both refund the agency and provide additional state funds to improve and protect election infrastructure. The catch lies in mostly Republican secretaries of state refusing to concede their security flaws and opting out of increased security precautions. Like Bella, begging for Edward’s vampire bite, they’re asking to be taken advantage of.

 Let’s first look at Moscow’s cyber hacking adventures. The FBI reported in August 2016 that hackers had been probing voter registration databases in almost 15 states. Georgia was not one of those states, although there is probably no way to know that given poor security safeguards and the state’s refusal to allow outside review of the system or assistance from Homeland Security to investigate or assist with security enhancements. Georgia’s story is instructive because it uses paperless voting machines like several other states which are both old, circa 2002 and known to have serious security concerns. However, state voting system officials are regularly asked to educate other states and even foreign countries.
Let’s first look at Moscow’s cyber hacking adventures. The FBI reported in August 2016 that hackers had been probing voter registration databases in almost 15 states. Georgia was not one of those states, although there is probably no way to know that given poor security safeguards and the state’s refusal to allow outside review of the system or assistance from Homeland Security to investigate or assist with security enhancements. Georgia’s story is instructive because it uses paperless voting machines like several other states which are both old, circa 2002 and known to have serious security concerns. However, state voting system officials are regularly asked to educate other states and even foreign countries. Donald Trump has promised to restore the country’s faith in elections, a faith that he was instrumental in destroying during a campaign where he consistently insinuated that the results would be rigged if he lost. He went as far as suggesting that he might not accept the elections results. Strangely, he concluded that the electoral process was indeed intact when he won, but his win, history making in his mind, was tainted by 3 million illegal voters who all voted for Clinton. Of course this fit neatly into Republican propaganda that has been charging voter fraud since Obama’s stinging victory in 2008, as a pretense for machinations that would restrict voters to those who support their party. Their instrument has been state voter IDs laws, literally written from templates distributed to state legislatures by The American Legislative Exchange Council (ALEC), a conservative organization financed by the Koch brothers. Legislatures have targeted minorities, the poor, the elderly and the young, groups that typically vote for Democrats and voted overwhelmingly for Obama in 2008 (oleblacklady/It turns out voting is a privilege).
Donald Trump has promised to restore the country’s faith in elections, a faith that he was instrumental in destroying during a campaign where he consistently insinuated that the results would be rigged if he lost. He went as far as suggesting that he might not accept the elections results. Strangely, he concluded that the electoral process was indeed intact when he won, but his win, history making in his mind, was tainted by 3 million illegal voters who all voted for Clinton. Of course this fit neatly into Republican propaganda that has been charging voter fraud since Obama’s stinging victory in 2008, as a pretense for machinations that would restrict voters to those who support their party. Their instrument has been state voter IDs laws, literally written from templates distributed to state legislatures by The American Legislative Exchange Council (ALEC), a conservative organization financed by the Koch brothers. Legislatures have targeted minorities, the poor, the elderly and the young, groups that typically vote for Democrats and voted overwhelmingly for Obama in 2008 (oleblacklady/It turns out voting is a privilege). 

 The mention of Comey transitioned to a discussion about Robert Mueller, another opportunity for Trump to get some licks into the campaign to discredit the special counsel he so didn’t want. The fact that Mueller was interviewed to replace Comey was cited as a conflict of interest. “There were many other conflicts that I haven’t said, but I will at some point.” Classic Trump, the innuendo of secret disclosures to come. He had a bone to pick as well, with assistant Attorney General Rosenstein, the guy who actually appointed Mr Mueller, suggesting that Rosenstein couldn’t be a loyal Republican, being from Baltimore, a predominantly Democratic city. He went further to cast a shadow on the wife of Andrew McCabe, the acting FBI director, whose wife received a donation from a Democratic PAC with ties to the Clintons in an unsuccessful Senate bid. Trump was using a broad brush to paint the investigation as rigged in Democratic efforts to dislodge him from the office.
The mention of Comey transitioned to a discussion about Robert Mueller, another opportunity for Trump to get some licks into the campaign to discredit the special counsel he so didn’t want. The fact that Mueller was interviewed to replace Comey was cited as a conflict of interest. “There were many other conflicts that I haven’t said, but I will at some point.” Classic Trump, the innuendo of secret disclosures to come. He had a bone to pick as well, with assistant Attorney General Rosenstein, the guy who actually appointed Mr Mueller, suggesting that Rosenstein couldn’t be a loyal Republican, being from Baltimore, a predominantly Democratic city. He went further to cast a shadow on the wife of Andrew McCabe, the acting FBI director, whose wife received a donation from a Democratic PAC with ties to the Clintons in an unsuccessful Senate bid. Trump was using a broad brush to paint the investigation as rigged in Democratic efforts to dislodge him from the office. 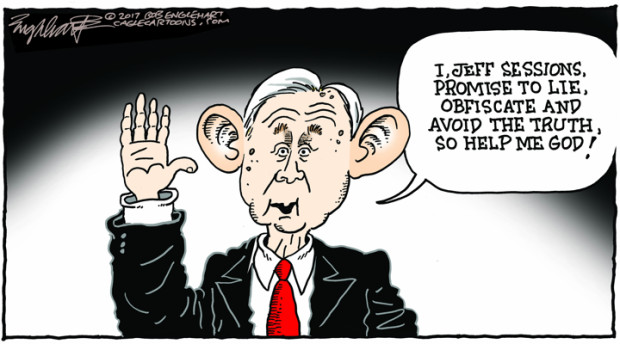

 The Hillary monkey on Trump’s back has poisoned the information well with supposed parallels that are wholly askew, a holdover from the pervasive mistrust that is the Clintons’ legacy since Bill won the White House. Trump has gone as far as reverse the narrative, telling evangelist Pat Robertson that Putin wanted Clinton to become president because she would have weakened the US military and increased energy prices in the US. An absurd fiction. It is well known that Putin shares the CelebrityPresident’s obsession with Hillary. Putin believes that Clinton, as Secretary of State, supported Russian protests during his last election campaign, an intervention from the US government in Russia’s “free” elections. His interventions for Trump were supersized vengeance against Hillary. The prospect that Trump would also be a disrupter of government, based on Russian intelligence research, was even more enticing.
The Hillary monkey on Trump’s back has poisoned the information well with supposed parallels that are wholly askew, a holdover from the pervasive mistrust that is the Clintons’ legacy since Bill won the White House. Trump has gone as far as reverse the narrative, telling evangelist Pat Robertson that Putin wanted Clinton to become president because she would have weakened the US military and increased energy prices in the US. An absurd fiction. It is well known that Putin shares the CelebrityPresident’s obsession with Hillary. Putin believes that Clinton, as Secretary of State, supported Russian protests during his last election campaign, an intervention from the US government in Russia’s “free” elections. His interventions for Trump were supersized vengeance against Hillary. The prospect that Trump would also be a disrupter of government, based on Russian intelligence research, was even more enticing. 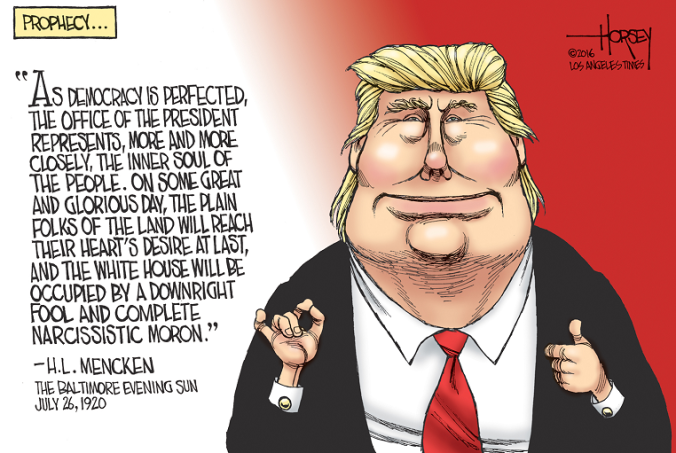 Domestically, chaos in the GOP has left a government completely controlled by one party mired in infighting. The government is still handcuffed, just as it was when the party stonewalled Obama at every turn. The president is a buffoon, more enamored with pretending to drive trucks than government. He consumes Russian “fake news” planted in cable TV from the online conservative media bubble and happily tweets it to the world. He deems Fox News a more credible source than US intelligence agencies, an opportunity for Putin to outmaneuver his blindfolded foe across the globe. A massive cloud of distrust hangs over our electoral process, Democrats convinced that ignored, Russians will continue to sully our electoral process. Republicans, embarking on a quest fired by the fake news of voter fraud, will quietly continue to limit the pool of eligible voters to those who will maintain their regime in power as they have been doing at the state level since 2000. (oleblacklady/
Domestically, chaos in the GOP has left a government completely controlled by one party mired in infighting. The government is still handcuffed, just as it was when the party stonewalled Obama at every turn. The president is a buffoon, more enamored with pretending to drive trucks than government. He consumes Russian “fake news” planted in cable TV from the online conservative media bubble and happily tweets it to the world. He deems Fox News a more credible source than US intelligence agencies, an opportunity for Putin to outmaneuver his blindfolded foe across the globe. A massive cloud of distrust hangs over our electoral process, Democrats convinced that ignored, Russians will continue to sully our electoral process. Republicans, embarking on a quest fired by the fake news of voter fraud, will quietly continue to limit the pool of eligible voters to those who will maintain their regime in power as they have been doing at the state level since 2000. (oleblacklady/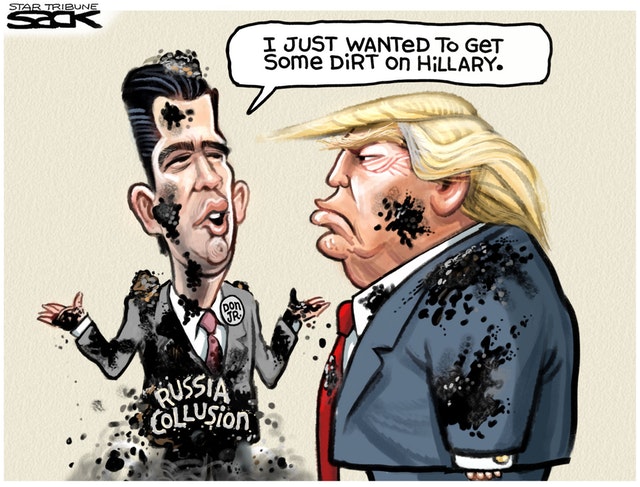
 That Russian businesses are intertwined with the Kremlin should come as no surprise. The Russian government can best be described as an authoritarian oligarchy, meaning all successful businessmen in Russia have some ties to the Putin government or they could not have achieved their success. Many in this group have ties to the KGB, Putin’s home before being catapulted to the head of the Russian government. Putin rewarded this group with economic favors precisely to consolidate and retain his political power. The group is relatively small but extremely loyal to their benefactor, strongly motivated by poverty with a fall from grace or alternatively, the threat of death for failure to comply. Thus any Russian businessman big enough to be doing business in the US have some links to the Kremlin.
That Russian businesses are intertwined with the Kremlin should come as no surprise. The Russian government can best be described as an authoritarian oligarchy, meaning all successful businessmen in Russia have some ties to the Putin government or they could not have achieved their success. Many in this group have ties to the KGB, Putin’s home before being catapulted to the head of the Russian government. Putin rewarded this group with economic favors precisely to consolidate and retain his political power. The group is relatively small but extremely loyal to their benefactor, strongly motivated by poverty with a fall from grace or alternatively, the threat of death for failure to comply. Thus any Russian businessman big enough to be doing business in the US have some links to the Kremlin. 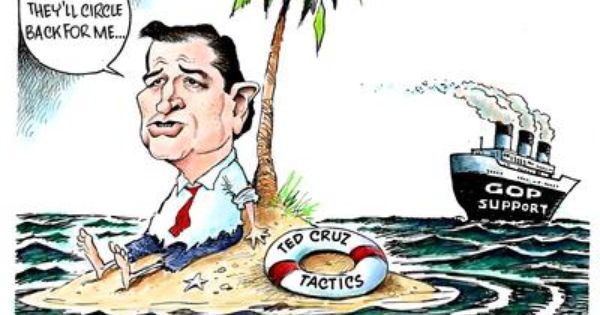
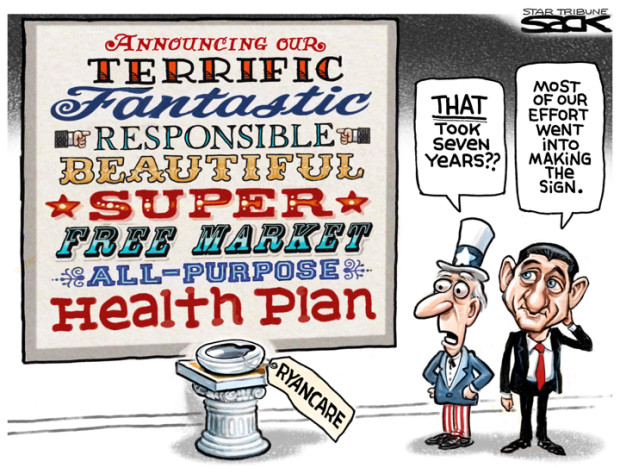
 Any good Republican will pass these situations off as opportunities for choice, like which hospital, the close one that I’ll have to pay for myself or the one that’s 20 miles away, where I’ll only have to pay the deductible and the co-pay. Or, after I pay food, rent/mortgage, car loan, household expenses, I can take the money I’m saving on a bare bones policy and plow that into a health savings account, so if I really do get sick and need an MRI or CT scan, I might be able to pay for it. Or I barely have enough money to pay routine costs of living so I’ll just cross my fingers and toes and refuse to get sick and opt out of insurance. All choices we’re dying to make, pun intended.
Any good Republican will pass these situations off as opportunities for choice, like which hospital, the close one that I’ll have to pay for myself or the one that’s 20 miles away, where I’ll only have to pay the deductible and the co-pay. Or, after I pay food, rent/mortgage, car loan, household expenses, I can take the money I’m saving on a bare bones policy and plow that into a health savings account, so if I really do get sick and need an MRI or CT scan, I might be able to pay for it. Or I barely have enough money to pay routine costs of living so I’ll just cross my fingers and toes and refuse to get sick and opt out of insurance. All choices we’re dying to make, pun intended. The outcry is building. Senator Susan Collins from Maine has publically announced she won’t vote for it. Rand Paul is still saying no and trying win others over. He thinks it’s still “Obamacare Light”, retaining the subsidies and many of the regulations. He doesn’t believe the government should be paying subsidies to an industry making $15 billion in a year. (Seems like a valid point.) That leaves only one lone wolf who can desert the pack if the bill is to pass. The governors, the AMA, various physician groups, American Hospital Association, and BlueCross BlueShield and insurance industry groups have all panned the bill. And the popular view is a resounding 17% of the public favor the bill. That should call for a Senate pause; apparently the outcry to Repeal Obamacare doesn’t actually exist. Obamacare may be failing (it isn’t but that is part of the GOP mantra), but people would rather have that than this bill. They did not ask for tax cuts for the wealthy at the expense of restructuring Medicaid. It’s difficult to recall an outcry across the country for Medicaid restructuring; in fact Trump promised during his campaign that he wouldn’t touch Medicaid and enough people voted for that to get him to the White House. Like most Trump’s statement, that one proved ephemeral; recently, he tweeted that Republicans should pass the bill. But that could change.
The outcry is building. Senator Susan Collins from Maine has publically announced she won’t vote for it. Rand Paul is still saying no and trying win others over. He thinks it’s still “Obamacare Light”, retaining the subsidies and many of the regulations. He doesn’t believe the government should be paying subsidies to an industry making $15 billion in a year. (Seems like a valid point.) That leaves only one lone wolf who can desert the pack if the bill is to pass. The governors, the AMA, various physician groups, American Hospital Association, and BlueCross BlueShield and insurance industry groups have all panned the bill. And the popular view is a resounding 17% of the public favor the bill. That should call for a Senate pause; apparently the outcry to Repeal Obamacare doesn’t actually exist. Obamacare may be failing (it isn’t but that is part of the GOP mantra), but people would rather have that than this bill. They did not ask for tax cuts for the wealthy at the expense of restructuring Medicaid. It’s difficult to recall an outcry across the country for Medicaid restructuring; in fact Trump promised during his campaign that he wouldn’t touch Medicaid and enough people voted for that to get him to the White House. Like most Trump’s statement, that one proved ephemeral; recently, he tweeted that Republicans should pass the bill. But that could change.
 This is just opposition research, Junior now contends, before the Russiamania. If David Koch had some dirt, that’s just the seedy side of campaigning in this day and age. As with most Trumpian dismissals, this is not NORMAL. The Russian government is another thing entirely. The fact that Donald Jr reported it to the campaign manager, Paul Manafort and the ever present Jared Kushner who both were willing to attend a meeting is a testament to successful grooming by Russian officials over years, at least since 2013 when the initial meetings took place. Soviet intelligence has perfected its espionage operations over decades; they’re so good that the contact may be completely unaware. But Junior’s enthusiastic uptake of the offer reflects something else, the absence of a moral compass, not surprising when your father has none either. He seemed neither surprised – ”What, the Russian government wants to help?” nor reluctant to cooperate, in other words, conspire. He had no understanding that it was inappropriate, dare we say unpatriotic; contacting the FBI never crossed his mind.
This is just opposition research, Junior now contends, before the Russiamania. If David Koch had some dirt, that’s just the seedy side of campaigning in this day and age. As with most Trumpian dismissals, this is not NORMAL. The Russian government is another thing entirely. The fact that Donald Jr reported it to the campaign manager, Paul Manafort and the ever present Jared Kushner who both were willing to attend a meeting is a testament to successful grooming by Russian officials over years, at least since 2013 when the initial meetings took place. Soviet intelligence has perfected its espionage operations over decades; they’re so good that the contact may be completely unaware. But Junior’s enthusiastic uptake of the offer reflects something else, the absence of a moral compass, not surprising when your father has none either. He seemed neither surprised – ”What, the Russian government wants to help?” nor reluctant to cooperate, in other words, conspire. He had no understanding that it was inappropriate, dare we say unpatriotic; contacting the FBI never crossed his mind.
 Jay walking seems to be a commonly used device to detain African Americans. In Sacremento, 50% of 200 tickets for jaywalking went to Black residents who make up 15% of the population. In Urbana, Illinois, 91% of jaywalking tickets went to African Americans who are 16% of the population. These statistics don’t lie. This is not a question of breaking the law, stop doing it. Who among the white citizenry hasn’t jaywalked or exceeded the speed limit? Can any of them imagine, even for a minute, that they would die for a speeding ticket. Everyone jaywalks, and yet Black people are the only cited ones repeatedly. Clearly, Black people are being targeted, orcas in a tank, plucked for one violation, thrown back in to be caught for another. Is it reasonable that most members of a community become burdened with fines? Is it just that those least able to pay are being asked to support local government? Just who is law enforcement serving and protecting if not themselves and a city council that refuses to invest money ripped from Black pockets in the communities. Are citizens safer or just poorer?
Jay walking seems to be a commonly used device to detain African Americans. In Sacremento, 50% of 200 tickets for jaywalking went to Black residents who make up 15% of the population. In Urbana, Illinois, 91% of jaywalking tickets went to African Americans who are 16% of the population. These statistics don’t lie. This is not a question of breaking the law, stop doing it. Who among the white citizenry hasn’t jaywalked or exceeded the speed limit? Can any of them imagine, even for a minute, that they would die for a speeding ticket. Everyone jaywalks, and yet Black people are the only cited ones repeatedly. Clearly, Black people are being targeted, orcas in a tank, plucked for one violation, thrown back in to be caught for another. Is it reasonable that most members of a community become burdened with fines? Is it just that those least able to pay are being asked to support local government? Just who is law enforcement serving and protecting if not themselves and a city council that refuses to invest money ripped from Black pockets in the communities. Are citizens safer or just poorer? And so we have Philando Castile, stopped more than 40 times in 13 years, driving with his family. Castile knew the drill; he was polite, respectful; he followed the officer’s instructions; he explained what he was doing. He broke no laws; – his gun was lawfully possessed. And he was gunned down while sitting in a car with his stepdaughter in the back seat by a cop because he “feared for his life”. What was the threat? The reasons given seemed to shift each time the cop gave another statement. At trial, he testified that he could tell Castile smoked marijuana, also legal but there was no way to know what the type of man who would smokes in front of his child would do to him. Clearly he and his lawyer worked it hard to rationale that fear alibi. During the stop, he told Philando he was stopped for a broken brake light; by the time of his interview the next day, he said he profiled him for resembling a suspect that went unidentified. There’s that resembling thing again. Seems like the cop just ran through an inventory of stuff to see what would stick. If he was really scared, won’t it have jumped out at him or was he trying to avoid the obvious, his primal fear of Black men. For most juries, contradictory testimony impugns the credibility of the witness, or at least that how it goes on TV. But law enforcement is special.
And so we have Philando Castile, stopped more than 40 times in 13 years, driving with his family. Castile knew the drill; he was polite, respectful; he followed the officer’s instructions; he explained what he was doing. He broke no laws; – his gun was lawfully possessed. And he was gunned down while sitting in a car with his stepdaughter in the back seat by a cop because he “feared for his life”. What was the threat? The reasons given seemed to shift each time the cop gave another statement. At trial, he testified that he could tell Castile smoked marijuana, also legal but there was no way to know what the type of man who would smokes in front of his child would do to him. Clearly he and his lawyer worked it hard to rationale that fear alibi. During the stop, he told Philando he was stopped for a broken brake light; by the time of his interview the next day, he said he profiled him for resembling a suspect that went unidentified. There’s that resembling thing again. Seems like the cop just ran through an inventory of stuff to see what would stick. If he was really scared, won’t it have jumped out at him or was he trying to avoid the obvious, his primal fear of Black men. For most juries, contradictory testimony impugns the credibility of the witness, or at least that how it goes on TV. But law enforcement is special.  The current outlook is bleak; there will be more Philando Castilles in years to come. Attorney General Sessions has taken steps back to the past – more and bigger jails, continued mandatory minimums and blindness to the discriminatory policing policies in the name of supporting the men in blue which has culminated in a rollback in Department of Justice investigations into complaints of police brutality and departmental procedures. Not coincidentally, law enforcement organizations were huge financial and elections supporters of Trump. Future investigations are unlikely and the DOJ has canceled or failed to pursue agreements that had already been negotiated under Loretta Lynch’s tenure as Attorney General. Law enforcement has refused to concede that harassment of African Americans that violates their civil rights is routine modus operandi, a given in the national approach to policing. Law enforcement departments, particularly smaller ones, are unlikely to abandon the use of traffic and pedestrian citations as cash cows. Addressing disparities in jury selection is not on any agenda. Without a national outcry, unlikely in the era of White America First, videos of cops murdering innocent Black men will continue, a drop in the
The current outlook is bleak; there will be more Philando Castilles in years to come. Attorney General Sessions has taken steps back to the past – more and bigger jails, continued mandatory minimums and blindness to the discriminatory policing policies in the name of supporting the men in blue which has culminated in a rollback in Department of Justice investigations into complaints of police brutality and departmental procedures. Not coincidentally, law enforcement organizations were huge financial and elections supporters of Trump. Future investigations are unlikely and the DOJ has canceled or failed to pursue agreements that had already been negotiated under Loretta Lynch’s tenure as Attorney General. Law enforcement has refused to concede that harassment of African Americans that violates their civil rights is routine modus operandi, a given in the national approach to policing. Law enforcement departments, particularly smaller ones, are unlikely to abandon the use of traffic and pedestrian citations as cash cows. Addressing disparities in jury selection is not on any agenda. Without a national outcry, unlikely in the era of White America First, videos of cops murdering innocent Black men will continue, a drop in the  The much anticipated (no more than by our President) meeting with Vladimir Putin has finally taken place. With the press just before the meeting, the two were all smiles. 45, sitting characteristically on the edge of his chair, leaned toward Putin. Putin, looking relaxed, leaned back in his. Much of the time, his eyes were downcast, never looking directly at Trump, not a gesture of humility but hubris, confident of control. Beside him, the CelebrityPresident reached for a hardy handshake, fawning, “It’s an honor to be with you”, a strange statement for an American defender of democracy to make about an ex-KGB officer whose troops are currently attacking Ukrainians, who imprisons his political opposition and sanctions the use of chemical weapons in Syria among other things. At one point, Putin leaned over to talk in Trump’s ear, asking according to Russian press, “These are the ones that insulted you?”, just to break the ice. Trump was overheard to reply, “You are right about that”. And they were off.
The much anticipated (no more than by our President) meeting with Vladimir Putin has finally taken place. With the press just before the meeting, the two were all smiles. 45, sitting characteristically on the edge of his chair, leaned toward Putin. Putin, looking relaxed, leaned back in his. Much of the time, his eyes were downcast, never looking directly at Trump, not a gesture of humility but hubris, confident of control. Beside him, the CelebrityPresident reached for a hardy handshake, fawning, “It’s an honor to be with you”, a strange statement for an American defender of democracy to make about an ex-KGB officer whose troops are currently attacking Ukrainians, who imprisons his political opposition and sanctions the use of chemical weapons in Syria among other things. At one point, Putin leaned over to talk in Trump’s ear, asking according to Russian press, “These are the ones that insulted you?”, just to break the ice. Trump was overheard to reply, “You are right about that”. And they were off. But here Putin sits, despite being kicked out of the G-8, accepted as an equal on the world stage. His Russia has been reestablished as a global power. He wanted his American adversary to stop meddling in his domestic affairs, as he completely believes Hillary Clinton did when Secretary of State by fomenting protest during his reelection. He wanted to be free of American criticism against his dictatorial government’s suppression of civil liberties and oligarchical corruption. He got no such freedom of that from 45’s predecessors, not Bush 43, not Obama. But in 45, he has the jackpot, even if it is of his own making. What an extraordinary statement to make about the country that used to be the leader of the free world!
But here Putin sits, despite being kicked out of the G-8, accepted as an equal on the world stage. His Russia has been reestablished as a global power. He wanted his American adversary to stop meddling in his domestic affairs, as he completely believes Hillary Clinton did when Secretary of State by fomenting protest during his reelection. He wanted to be free of American criticism against his dictatorial government’s suppression of civil liberties and oligarchical corruption. He got no such freedom of that from 45’s predecessors, not Bush 43, not Obama. But in 45, he has the jackpot, even if it is of his own making. What an extraordinary statement to make about the country that used to be the leader of the free world!